I recently contributed this article to a Tech Magazine. But due to obvious reasons the article was edited and few of the screenshots were dropped. Though I completely realized why it was done and understand the necessity of doing the same. I thought to post the unedited version on my blog for those with tough hearts!!
Have Fun !!
Let’s start this article with a quick quiz. Now there is no direct award for this quiz. But believe me, if you answer the questions right. By the end of this article you will feel much secure. But if you don’t. Then get ready for a horror story.
Here is the quiz.
1. Do you remember the exact link of your online banking website? For instance the ICICI Bank’s online banking login page?
2. Do you remember, who is the SSL Certificate Signing authority of most of the online services where you do online monitory transactions?
Most likely the answer will be a “No”. If not for the question No. 1, but for Question No. 2, I am pretty sure. This is because I myself don’t remember the SSL Signing authorities for most of the websites I use for monitory transactions.
Now, why am I asking this is to illustrate on a very dangerous, and most often targeted online hacking attack. This attack is more like a mix of many hacking techniques but is one of the most successful. If you are an old PCQuest reader. You might remember way back in July 2005 I did a story for PCQuest on how someone can do a DNS poisoning attack and phish any banking website from within a LAN and steal passwords. The only way for a smart user to save himself/herself was by making sure not to proceed on a link when there is a SSL Certificate warning. You can read that article here
http://www.pcquest.com/pcquest/news/177727/real-fake
But today, things are different. The banking websites like ICICIBank have come a long way securing their websites from virtually any kind of attacks by using multiple levels of authentication and very secure code practices. But not all transaction websites are that save. For that matter, even today as well ICICI Bank website can also be phished. And if the user accessing the website is not smart enough. There is a complete possibility that a certain share of his/her financial information could be hacked or stolen.
Thought it’s difficult for a hacker to actually go ahead and do transaction on victims behalf due the multi-level authentication required for such banks. And the Hacker would need to copy/clone the victim’s debit card, mobile number, and steal both the login and transaction password for a successful transaction.
But getting into victims account and checking his A/C details should be cake walk. Also, to scare you more. Not all banks with online banking have multi-level authentication. Forget the third party payment processing websites and ecommerce sites where you go and disclose your credit/debit card information.
Ok, now let’s take a simple scenario and see how such things are possible. In this article we will try to make sure we do not disclose actual steps of hacking and phishing. But for explanation purposes we might be discussing some actual tools and techniques used by hackers. So, please “Don’t Try This at Home“.
And if you do, you are solely responsible for any legal implications followed.
So, let’s assume one fine day you reach your office. Open you laptop and remember you need to pay your mobile phone bill. You quickly logging to *http://icicibank.com and proceed towards the login page.
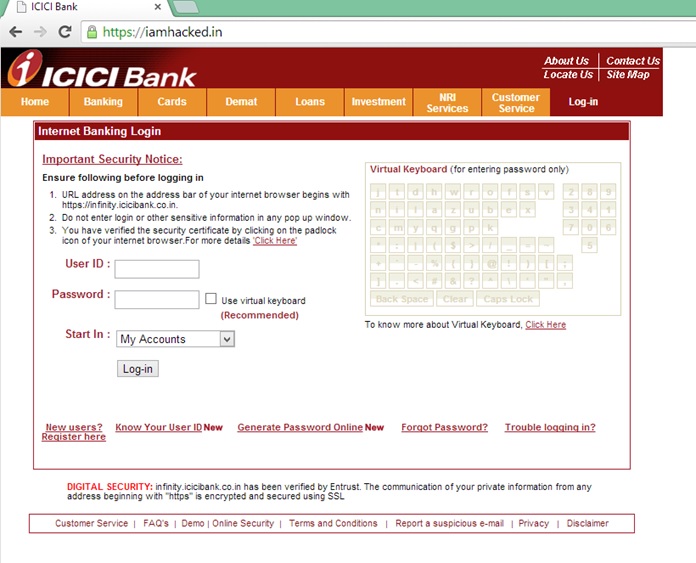
When the login page pops up, you see the exact same page which you have been seeing every day. The page also shows a valid https certificate. But hey, wait a second! What’s with the domain name? The domain name says http://iamhacked.in !!!
You get the scariest chills and kill the browser and rush to your Company’s System/Network/Security Administrator.
Not such a bad end of the story. Right? Now let’s assume the domain name was https://infinity-icicibank.co.in. Instead of the actual ICICI bank login page FQDN, i.e. – https://infinity.icicibank.co.in. Would you have noticed and rushed to the System Administrator?
May be not!! And to scare you more. While writing this article, Infinity-icicibank.co.in is available for purchase by any hacker for 199/- INR.

Now, let’s try to understand how exactly such a thing could have happened. Such an attack is essentially a combination of social engineering, Phishing, arp spoofing and dns poisoning. Now let’s elaborate on it a bit.
Social Engineering
In simpler terms, Social Engineering is nothing but ways of conning people. Online or Offline. And there are many ways for doing so. The trick used here is simple. Technically you can get a valid SSL certificate for any domain you own. So a hacker could easily go, book a similar sounding/looking domain to the website he is trying to Phish.
And then he can get a SSL certificate generated for the same. There are many small and big SSL certificate signing authorities. For our demo, we used a signing authority called Start SSL – http://startssl.com/. Here you can actually get a SSL certificate for any domain for free. And this certificates are valid on most of the recent web browsers.
So, we went ahead, book the domain iamhacked.in and got a valid SSL certificate for it in no time. We could have happily booked infinity-icicibank.co.in as well. But we didn’t just because we are not here to do actual phishing attack. But yes. Someone can do it any day.
Phishing
Phishing is basically cloning a website and make sure it looks identical to the original. Just that, when someone puts his credentials, its actually sent to the hacker and the user is either shown a genuine looking error message or he is actually forwarded to the original website, to make sure the user never realizes he is been hacked.
We used a simple tool called SET or Social Engineering Toolkit, installed it on a free Amazon Cloud instance to create the ICICI Bank’s clone website. And believe me after SET is installed. It takes exactly 4 click and a Shift + Insert ( to past the original website’s link to be cloned ) to create a clone of any website along with a script to harvest credentials. We will not go into how to do it because of obvious reasons. But yeah, you can take my words. It’s easy and a simple google search will give you ample material for this.
ARP Spoofing
This is one of the weirdest hack. It’s not weird because it’s dangerous or something. This is weird because this uses one of the oldest vulnerability in Ethernet switches. And still this is prominently widespread in today’s corporate networks. Even in most of the cases this goes undetected. Recently we saw this attack to go undetected in a network where a Cyberoam UTM was used for security. On raising this issue, cyberoam informed us that such attacks are not handled or detected by its IDS. And the only way of securing your network against this is by setting up MAC address restrictions. Which for a large network might not be feasible. And it’s not just Cyberoam, most of the SMB class UTMs are incapable of handling such attacks
Now, let’s try to quickly understand what ARP Spoofing is. By using an Arp Spoofing attack. An attacker can change the ARP-IP table in the Ethernet switches’ cache and make sure the data intended for the victim’s machine reaches the hacker’s machine. And once the data is captured by the hacker, it’s forwarded to the victim, to make sure the intended data flow is not hindered. This is also known as Man in the middle attack. So, in our scenario, what we did was, we spoofed the IP address the internet gateway and made sure any data sent to the internet is first logged to the hacker’s machine and then forwarded out.
DNS Poisoning
This technique essentially relies on ARP Spoofing and when all the outbound data is intercepted by the hacking machine. It manipulates the UDP requests generated for DNS querying and changes the destination IP of any Domain name. So, it’s more like the Hosts file. But acts for the entire network without specifically hacking a client machine. And exactly like the Hosts file it lets you override the actual Domain name resolution and force the DNS request to return a fake value.
So for instance, with the help of DNS Poisoning, you can return “127.0.0.1” as the IP address for google.com. In our scenario, we forwarded our request for infinity.icicibank.co.in to our hacking machine’s IP address sitting on the AWS Cloud. And we ran a simple web redirect on the hacking machine to forward the IP address to our own domain name https://iamhacked.in !!
Wasn’t it Simple?
How to save yourself
Now, it will be completely impractical to just scare you and not to tell you how you can safeguard yourself from such attacks. Basically, there is no technical way of doing it in most of the cases. And it’s mostly all about best practices. And here is a quick list.
1. Never ever do only transaction from an unknown or public network. Even try to avoid office networks. Coffee Shops and Cyber Cafés are a strict No No. Your home would be the safest bet. ARP and dns poisoning is mostly not possible on Wi-Fi connections. And then there are limited number of users in your home Wi-Fi making it much safer.
2. Always. Yes, always try to remember the actual links of your banking website. If not easy to remember. Just note it down and make sure it’s the same whenever you access it. In case you see even a minor change. Call you bank or financial institution to verify.
3. Check for the SSL Certificate. If you see an error like the below error. Run for your life.

4. It might sound going a bit too far and feeling a bit paranoid. But as they say. Only Paranoid’s survive. You should also note down the SSL Certificate signing authority for all your monitory related websites. And tally it whenever you are revisiting the website. If it’s a decently secure website it must have the SSL Certificate signed by the top few signing authorities such as GlobalSign, Verisign, Thawte and Geotrust. But if you see an SSL Certificate signed by some other very smaller certificate signatories like the one we used in our test, Star SSL. It’s good to be a bit cautions and call up the website’s call center to verify.
5. A website with Vetted Certificated is much trusted. When you see the green bar on the address bar while accessing an HTTPS page, its means the sites uses a validated certificate. This means the certificate signing authority has vetted the existence and validity of the organization and chances of it being fake is near to zero.
6. This one is for the Sysadmins. You might be using an UTM or an IDS/IPS system. Please check with the vendor if the system blocks or at least detects and alerts ARP Spoofing attacks. If they do, great!! Else just use a tool call arpwatch. This will keep sending you alert mails if in case your network is attacked by ARP Spoofing. You can read on how to setup arpwatch at http://www.pcquest.com/pcquest/news/176927/tools-counter-hack-attack
*The name of ICICI Bank used here is just for explanation purpose, as this is one of the widely used Online Banking website in India. We here are not at all trying to demonstrate any weakness or vulnerability in ICICI Bank’s website. Rather we believe ICICI Bank provides one of the most secure online banking experience. And the hacking attempt discussed in this article are applicable on every online bank or for that matter every online transaction website.


Hi Anindya,
Thanks for sharing the valuable information. Also you suggested to go for Linux machine for all Financials/social media using DSL+WiFi Router, just wanted to check if Mac Laptop and iOS devices are also that much safe.
Will wait for your reply…
Hi Nitin,
Thanks for the comment. But you actually asked a very interesting question. And that points to the fact that I didn’t clarified why I asked everyone to go for a Linux Laptop. So let me do that here.
As an OS, non are extraordinarily unsafe. be it any recent Linux, Windows or Mac version. But the fact that we are most comfortable using and misusing Windows, is what makes it unsafe.
Its a matter of fact that many Windows machines around will be running on a Pirated Windows Version or at least there will be one pirated applications installed. which is one of the key cause of Windows environment becoming unsafe for financial uses. And then, we are so comfortable downloading and installing freeware/shareware apps from whatever site we see on a Google search on Windows, is another major coz
With Linux. the piracy issue is anyways solved. Because the OS is free and most of the applications you will be using, will be straight from the OS’s own repository. even the same reason goes for lesser number of malwares. Whatever you need is just a yum or apt-get away. The reason of recommending Linux was also because, it being slight unfamiliar for basic users, the chance that they will be using it for too many non crucial things is limited. Which will keep the machine safe and isolated for only doing high security tasks
So, now coming back to your question. Mac is again as safe as the most week applications you have installed on your Mac. I myself use a Windows machine for my regular use. And I feel pretty safe with not a single pirated app on it.
Hope that answers your question.
Cheers,
Roy
That was a good story. You had me spooked, but the ghossts
were a nice bunch.